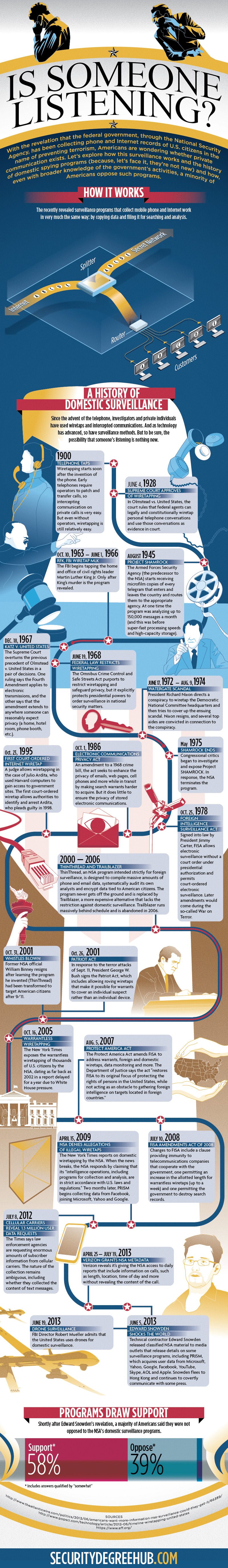
Domestic Spying: Is Someone Listening graphic explores domestic surveillance and the history of domestic spying in the US.
With the revelation that the federal government, through the National Security Agency, has been collecting phone and Internet records of U.S. citizens in the name of preventing terrorism, Americans are wondering whether private communication exists. Let’s explore how this surveillance works and the history of domestic spying programs (because, let’s face it, they’re not new) and how, even with broader knowledge of the government’s activities, a minority of Americans oppose such programs.
How It Works
The recently revealed surveillance programs that collect mobile phone and Internet work in very much the same way: by copying data and filing it for searching and analysis.
A History of Domestic Surveillance
Since the advent of the telephone, investigators and private individuals have used wiretaps and intercepted communications. And as technology has advanced, so have surveillance methods. But to be sure, the possibility that someone’s listening is nothing new.
1900 – Telephone taps
Wiretapping starts soon after the invention of the phone. Early telephones require operators to patch and transfer calls, so intercepting communication on private calls is very easy. But even without operators, wiretapping is still relatively easy.
June 4, 1928 – Supreme Court approves of wiretapping
In Olmstead v. United States, the court rules that federal agents can legally and constitutionally wiretap personal telephone conversations and use those conversations as evidence in court.
August 1945 – Project SHAMROCK
The Armed Forces Security Agency (the predecessor to the NSA) starts receiving microfilm copies of every telegram that enters and leaves the country and routes them to the appropriate agency. At one time the program was analyzing up to 150,000 messages a month (and this was before super-fast processing speeds and high-capacity storage).
Oct. 10, 1963–June 1, 1966 – RFK, FBI Wiretap MLK
The FBI begins tapping the home and office of civil rights leader Martin Luther King Jr. Only after King’s murder is the program revealed.
Dec. 18, 1967 – Katz v. United States
The Supreme Court overturns the previous precedent of Olmstead v. United States in a pair of decisions. One ruling says the Fourth Amendment applies to electronic transmissions, and the other says that the amendment extends to anywhere someone can reasonably expect privacy (a home, hotel room, phone booth, etc.).
June 19, 1968 – Federal law restricts wiretapping
The Omnibus Crime Control and Safe Streets Act purports to restrict wiretapping and safeguard privacy, but it explicitly protects presidential powers to order surveillance in national security matters.
June 17, 1972–Aug. 9, 1974 – Watergate scandal
President Richard Nixon directs a conspiracy to wiretap the Democratic National Committee headquarters and then tries to cover up the ensuing scandal. Nixon resigns, and several top aides are convicted in connection to the conspiracy.
May 1975
Congressional critics began to investigate and expose Project SHAMROCK. In response, the NSA terminates the program.
Oct. 25, 1978 – Foreign Intelligence Surveillance Act
Signed into law by President Jimmy Carter, FISA allows electronic surveillance without a court order under presidential authorization and permits court-ordered electronic surveillance. Later amendments would come during the so-called War on Terror.
Oct. 1, 1986 – Electronic Communications Privacy Act
An amendment to a 1968 crime bill, the act seeks to enhance the privacy of emails, web pages, and cell phones and more while in transit by making search warrants harder to acquire. But it does little to ensure the privacy of stored electronic communications.
Oct. 23, 1995 – First court-ordered Internet wiretap
A judge allows wiretapping in the case of Julio Ardita, who used Harvard computers to gain access to government sites. The first court-ordered wiretap allows authorities to identify and arrest Ardita, who pleads guilty in 1998.
2000 — 2006 – ThinThread and Trailblazer
ThinThread, an NSA program intended strictly for foreign surveillance, is designed to compile massive amounts of phone and email data, systematically audit its own analysts and encrypt data tied to American citizens. The program never gets off the ground and is replaced by Trailblazer, a more expensive alternative that lacks the restriction against domestic surveillance. Trailblazer runs massively behind schedule and is abandoned in 2006.
Oct. 26, 2001 – Patriot Act
In response to the terror attacks of Sept. 11, President George W. Bush signs the Patriot Act, which includes allowing roving wiretaps that make it possible for warrants to cover an individual suspect rather than an individual device.
Oct. 31, 2001 – Whistles blown
Former NSA official William Binney resigns after learning the program he invented (ThinThread) had been transformed to target American citizens after 9/11.
Oct. 16, 2005 – Warrantless wiretapping
The New York Times exposes the warrantless wiretapping of thousands of U.S. citizens by the NSA, dating as far back as 2002 in a report delayed for a year due to White House pressure.
Aug. 5, 2007 – Protect America Act
The Protect America Act amends FISA to address warrants, foreign and domestic wiretaps, data monitoring and more. The Department of Justice says the act “restores FISA to its original focus of protecting the rights of persons in the United States, while not acting as an obstacle to gathering foreign intelligence on targets located in foreign countries.”
July 10, 2008
FISA Amendments Act of 2008
Changes to FISA include a clause providing immunity to telecommunications companies that cooperate with the government, one permitting an increase in the allotted length for warrantless wiretaps (up to a week) and one permitting the government to destroy search records.
April 15, 2009 – NSA denies allegations of illegal wiretaps
The New York Times reports on domestic wiretapping by the NSA. When the news breaks, the NSA responds by claiming that its “intelligence operations, including programs for collection and analysis, are in strict accordance with U.S. laws and regulations.” Two months later, PRISM begins collecting data from Facebook, joining Microsoft, Yahoo! and Google.
July 8, 2012 – Cellular carriers reveal 1.3 million user data requests
The Times says law enforcement agencies are requesting enormous amounts of subscriber information from cellular carriers. The nature of the collection remains ambiguous, including whether they collected the content of text messages.
April 25, 2013 — July 19, 2013 – Verizon grants NSA metadata
Verizon reveals it’s giving the NSA access to daily reports that include information on calls, such as length, location, time of day and more without revealing the content of the call.
June 5, 2013 – Edward Snowden shocks the world
Technical contractor Edward Snowden released classified NSA material to media outlets that release details on some surveillance programs, including PRISM, which acquires user data from Microsoft, Yahoo, Google, Facebook, YouTube, Skype, AOL and Apple. Snowden flees to Hong Kong and continues to covertly communicate with some press.
June 19, 2013 – Drone surveillance
FBI Director Robert Mueller admits that the United States uses drones for domestic surveillance.
Programs Draw Support
Shortly after Edward Snowden’s revelation, a majority of Americans said they were not opposed to the NSA’s domestic surveillance programs.
Support* Oppose*
58% 39%
* Includes answers qualified by “somewhat”
Related:
- Top 20 Online Cyber Security Degree Programs
- 10 Online Homeland Security Degree Programs
- Top 10 Online Network Security Degree Programs